BUSINESS
Gnsoft offers the entire system, from planning to developing and deploying information systems
that your environment needs most
De-identification of personal information
Through preliminary review, we determine whether the data constitutes personal information. We then de-identify the data to ensure that individuals cannot be recognized. The de-identified information is evaluated to determine if it can be re-identified when combined with other information. If deemed appropriate, it is considered de-identified information. Finally, necessary measures are taken to prevent re-identification during the use of de-identified information, ensuring post-management.
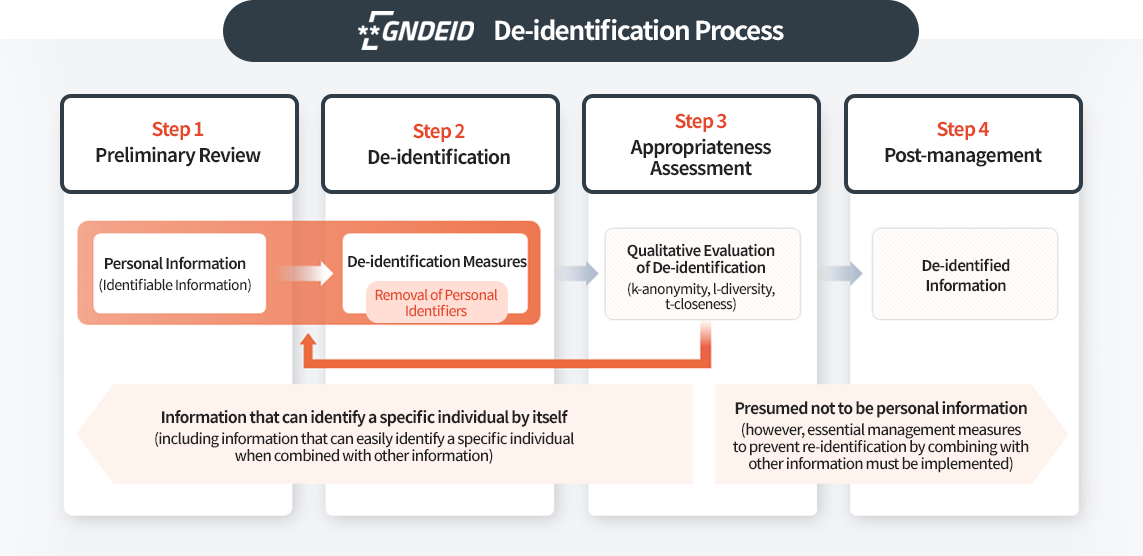
De-identification Process:
Step 1: Preliminary Review
Step 2: De-identification
Step 3: Appropriateness Assessment
Step 4: Post-management
Personal Information (Identifiable Information), De-identification Measures (Removal of Personal Identifiers), Qualitative Evaluation of De-identification (k-anonymity, l-diversity, t-closeness), De-identified Information, Appropriate, Inappropriate Information that can identify a specific individual by itself (including information that can easily identify a specific individual when combined with other information) Presumed not to be personal information (however, essential management measures to prevent re-identification by combining with other information must be implemented)
Characteristics of GN-DEID
Advantages
-
Personal Data De-identification Measures
Features and configuration compliant with de-identification guidelines- Provides optimized UI functions for each step of the 'Personal Data De-identification Guidelines': preliminary review, de-identification measures, and adequacy assessment
- Offers de-identification techniques as specified in the 'Personal Data De-identification Guidelines'
- Provides functions for checking the re-identification risk using privacy protection models (k-anonymity, l-diversity, t-closeness)
-
Various Forms of Personal Data De-identification Functions
- Enables detection and de-identification measures for personal data not only in structured data but also in unstructured data by extending detection technology to cover unstructured data
-
User Convenience Features During the Process
- Offers automation functions that automatically set data types when data is uploaded
- Provides a preview feature to check data before and after de-identification
- Displays result messages to show whether de-identification measures were successful and indicates locations of abnormal data
-
High-Speed De-identification Processing Technology
- Enhances processing speed for large-scale personal data de-identification processes by storing original data in memory
-
Adequacy Review Function for De-identification Results
- During the adequacy assessment phase according to the 'Personal Data De-identification Guidelines', provides an adequacy review function using k-anonymity as a base, and additionally l-diversity and t-closeness if necessary